Incident Management Process
Incident management processes address threats, ensure communication protocols, and return your business to operational normalcy.
What Is Incident Management?
Incident management refers to an organization's process of discovering, assessing, addressing, and reporting incidents. The nature of incidents can vary, but in all cases, they involve the potential damage or disruption of an organization's critical assets and/or operations. Without rapid mitigation, incidents can escalate to become disastrous. Any incident management process aims to return the business to operational normalcy, repair any damage, and follow communication protocols internally and externally. You can read more on the topic on TechTarget.com.
An incident management system is vital to ensure that minor problems don’t become large problems and that significant problems don’t become catastrophes. A proper incident management process is vital for a business of any size. Errors happen, unforeseen problems arise, and people make mistakes. An incident management process is designed to prevent everyday issues from having wide-ranging effects.
While often correlated with IT/ITIL, incident management and incident response processes are needed across an organization. Some examples of incidents requiring a coordinated, consistent, and rapid response include:
- Cyberattacks
- Privacy Breaches
- Natural Disasters
- At-Risk Employee Terminations
- Public Relations Crises
- Product Recalls
In all cases, an event trigger is followed by a well-executed, cross-departmental incident management process or "Runbook" that a formal or informal Incident Response Team handles. Each team member is responsible for specific incident mitigation activities and knows how and when to escalate to another team or team member. An incident management system should be practiced with well-documented duties so that nothing falls through the cracks.
At the end of the incident management process, a response assessment reviews what happened, response performance, and results against Service Level Objectives (SLOs). By recording and documenting each incident, the incident management process can be improved, and lessons can be learned for future incident management situations.
Sample Incident Management Process
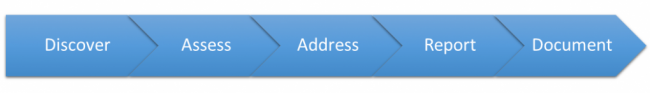
For a visual example of laying out an incident response process, check out this guide from LucidChart.
Why Automate the Incident Management Process?
Everyone has been part of a "fire drill" approach to handling an incident. In some cases, individuals step up and guide the incident management response, acting as a traffic cop and doing their best to both communicate and manage activities. However, even in the best situation with the best traffic cops, the response tends to be slower and less effective than it should be. In some cases, these delays and missteps can cost an organization greatly both in terms of revenue and reputation.
What is the advantage of an automated incident management process in this case? Imagine that rather than leaving things to individual traffic cops, every driver on the road was getting personalized instructions for what they should be doing. You can imagine how much more quickly the incident would be resolved!
With this in mind, incident management software that automates your incident response can seem like a no-brainer.
Automating the incident management process as much as possible will:
- Shorten incident response time and cycles
- Ensure resources are appropriately used and involved
- Reduce human error
- Allow the response team to focus on the task at hand
- Provide an audit trail of all response activities
- Improve communication
Centralized Incident Management Governance
Having a centralized incident reporting system accessible to log incidents consistently and route them to trained personnel for the initial assessment is the first step. This alone could help ensure a rapid, more coordinated response to security incidents by providing runbooks for performing actions and communicating status.
Once reported, incidents can be prioritized based on reporting time or determining severity. While all incidents are logged and analyzed, "Critical" incidents might be routed immediately to the highest-level remediation team and key executives. In addition, an alert might be sent back to the originator for immediate clarification and additional information. If a "Critical" incident has not had action taken within 5 minutes, it could escalate to another team, fire off more alerts, etc.
Incident Management Response Workflow Example

Real-World Incident Management and Response Examples
Using our low-code workflow automation platform, our customers have built incident management systems to handle various incident response needs. The example below is from a Privacy Incident system that one of our customers developed to handle potential privacy breaches. Anyone in the organization can submit an incident report, and the response workflow is immediately kicked off.
Note: We're only showing part of the system to maintain anonymity. The complexity of the process is well beyond what you see here.

Response Audit Traceability
An incident response audit trail is critical to response process improvement and identifying bottlenecks, dropped hand-offs, and turnaround time issues.
Best-practice audit trails include:
- Verifiable evidence can be presented internally or externally.
- The exact sequence of tasks or activities that have been performed.
- What actions were taken or not taken.
- Information about who performed each task(s).
- Time and date stamps for all activities.
Audit trails, therefore, explicitly provide “who, what, when, where, how” information that can be used to confirm that tasks were performed as expected or identify errors. Audit reports can show examples of areas for improvement in an incident management process. For instance, if there are frequent mistakes or delays unearthed by reviewing the data, workflow administrators can look for opportunities to improve forms, copy, routing, etc., and ensure a better end product.
How Can Integrify Help Your Incident Management System?
Integrify provides incident management software that allows our customers to build customized, automated response processes based on any incident, whether it's a cyberattack, HR issue, or any other kind of incident in need of a coordinated, rapid response. Our software is proven in the field and has been used by some of the largest companies in the world, including GlaxoSmithKline, Sony, AT&T, and BP.
The Tools to Ensure Rapid Incident Response
Our visual process designer interface lets you design custom access request workflows using drag and drop. Automatically assign tasks and route information based on your organization's unique workflow. Set alerts, reminders, and escalations to keep work moving forward.
Form Designer
Easily create responsive, Web-based forms to capture incident information. Include various field types, form logic, templates, and layouts to ensure the correct data is captured and routed every time.
Self-Service Portal
Provide a unified front-end experience that allows users to submit incident reports, complete reviews, and track incident status. Collaborate in real-time about work being performed. Provide visibility by role to see which tasks are completed, pending, or in progress for a great user experience.
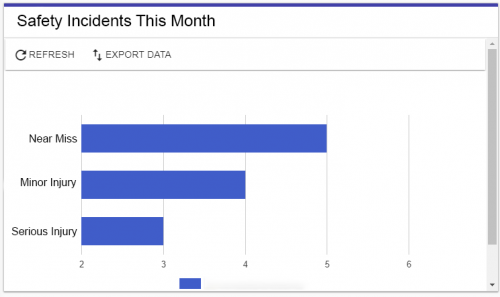
Incident Process Reporting
Track and maintain an audit trail of all your incident response workflows, including incident form data, remediation activities, and resolutions. Follow team progress and use KPI scoreboards to track the overall efficiency and drive improvements. Build custom reports to analyze and share with stakeholders.
Process Integration (API)
Create workflow applications with process integration into existing enterprise systems and messaging platforms like Slack. Our open architecture and standalone web service allow other applications to initiate a workflow, complete a list of tasks, update process statuses, and conduct other bi-directional activities. Connect everything with Integrify.
Interested in Automating Your Incident Management Workflow?
We have resources to help you investigate, plan, and implement an automated incident management workflow.

Automate Any Incident Process
To see how quickly you can begin automating your business processes, request a demonstration or trial of Integrify.
Features
- Capture incident details
- Assign tasks to team members
- Add alerts, reminders, escalations
- Capture remediation activities
- Provide auditable retrospectives

